This post is to demonstrate the process to Configure FileZilla FTP Server with Fortigate Firewall.
FileZilla Server configuration
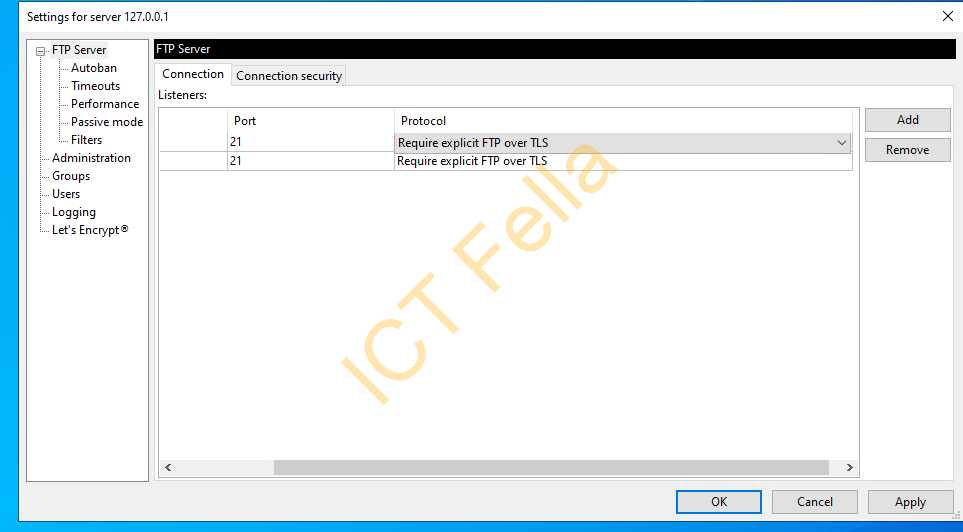
Connection configuration
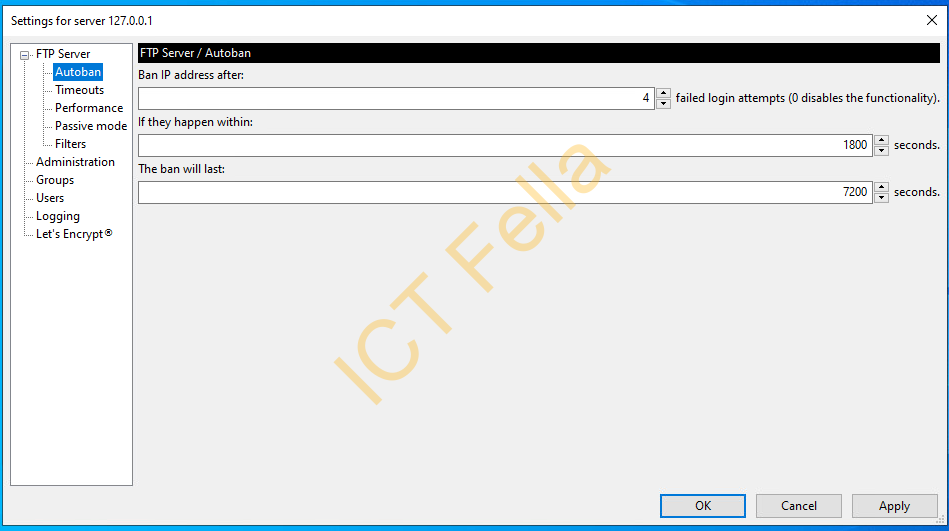
Auto-ban configuration
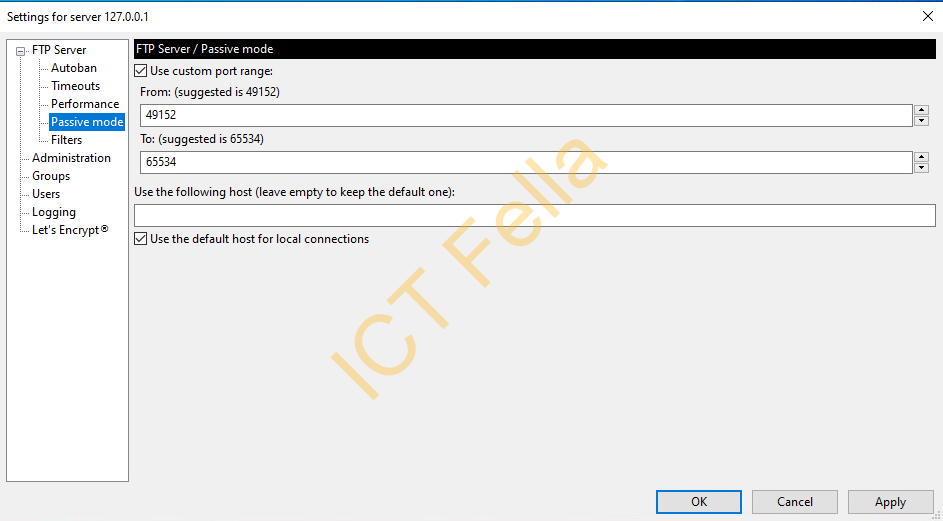
Passive mode port range
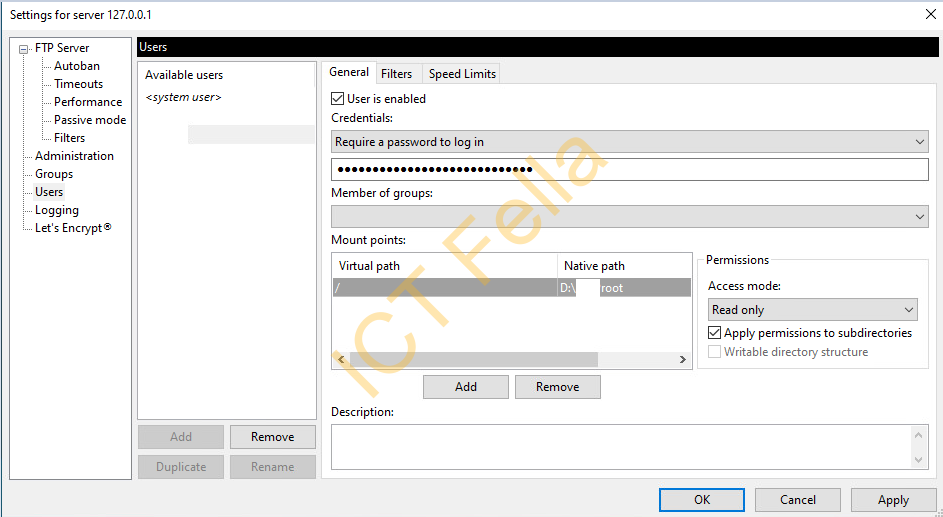
FTP user configuration
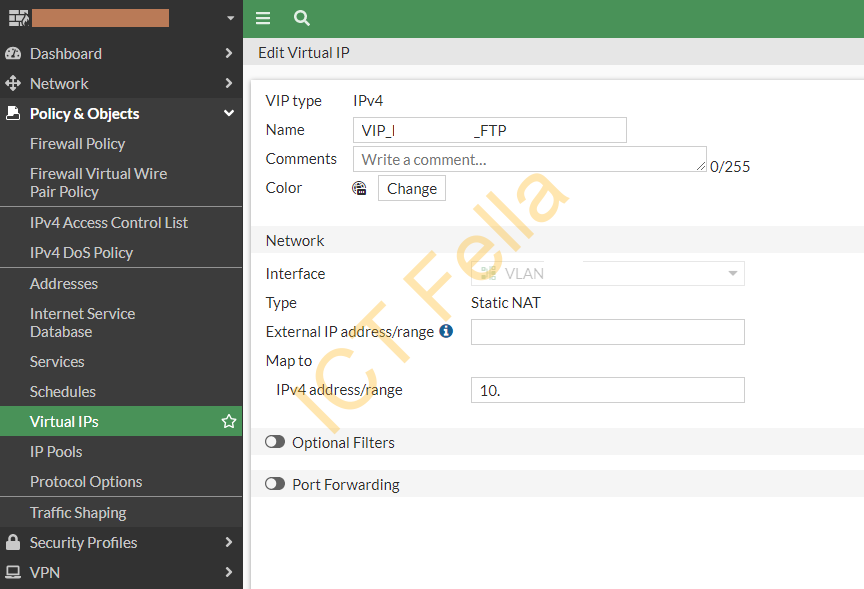
Fortinet FortiGate Firewall configuration
In virtual IP configuration, we have dedicated public IP, hence 1 to 1 Static NAT is used
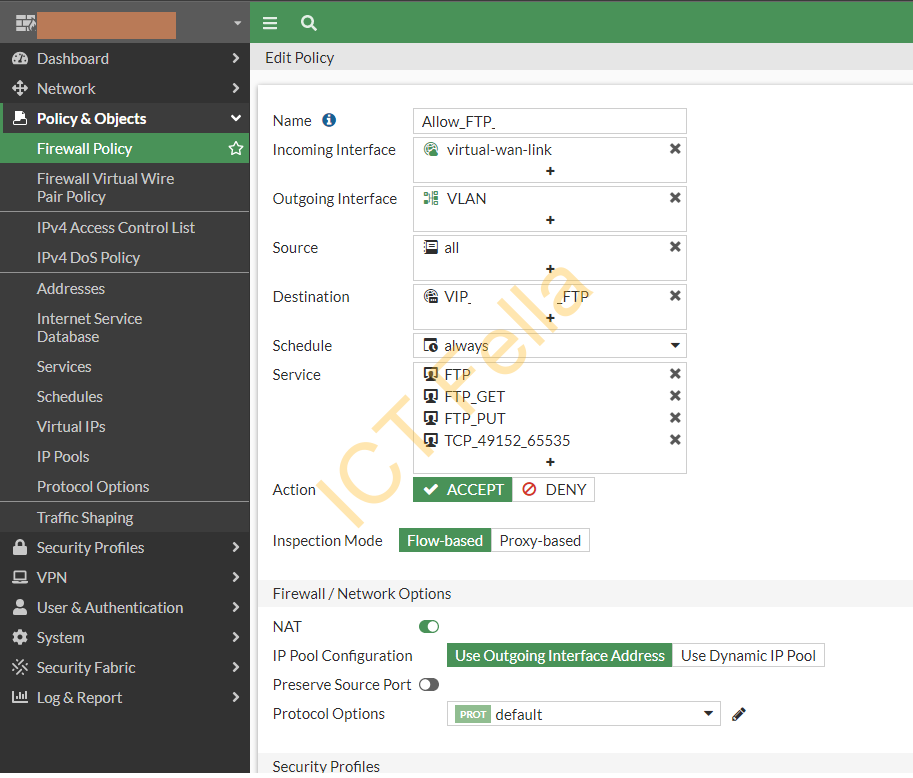
Firewall Policy configuration
Common Error
Server sent passive reply with unroutable address. using server address instead.
Error is caused by “passive mode” FTP, the negotiated ports are not open in this case after initial authentication. Define the port range in both the FTP server and FortiGate firewall to fix the problem.
Useful link
Network Configuration – FileZilla Wiki (filezilla-project.org)
